A Hybridized- Logistic Regression and Deep Learning-based Approaches for Precise Anomaly Detection in Cloud
Main Article Content
Abstract
Anomaly Detection plays a pivot role in determining the abnormal behaviour in the cloud domain. The objective of the manuscript is to present two approaches for Precise Anomaly Detection Approaches by hybridizing RBM with LR and SVM models. The various phases in the present approach are (a) Data collection (b) Pre-processing and normalization; OneHot Encoder for converting categorical values to numerical values followed by encoding the binary features through normalization (c) training the data (d) Building the Feedforward Deep Belief Network (EDBN) using hybridizing Restricted Boltzmann Machine (RBM) with Logistic Regression (LR) and Support Vector Machine (SVM); In the first approach, RBM model is trained through unsupervised pre-training followed by fine-tuning using LR model. In the later approach, RBM model is trained through unsupervised pre-training followed by fine-tuning using SVM model; both the approaches adopt unsupervised pre-training followed by supervised-fine-tuning operations (e) Model Evaluation using the significant parameters such as Precision, Recall, Accuracy, F1-score and Confusion Matrix. The experimental evaluations concluded the effective anomaly detection techniques by integrating the RBM with LR and SVM for capturing the intricate patterns and complex relationships among the data. The proposed approaches paves a path to improved anomaly detection technique, thereby enhancing the security features and anomaly monitoring systems across distinct domains.
Article Details
References
Weipeng Gao, Youchan Zhu, “A Cloud Computing Fault Detection Method Based on Deep Learning,” Journal of Computer and Communications, vol. 05, no. 12, pp. 24-34, 2017, DOI: 10.4236/jcc.2017.512003.
S. Garg, K. Kaur, N. Kumar, G. Kaddoum, A. Y. Zomaya, and R. Ranjan, “A hybrid deep learning-based model for anomaly detection in cloud datacenter networks,” IEEE Transactions on Network and Service Management, vol. 16, no. 3, pp. 924-935, 2019, DOI: 10.1109/TNSM.2019.2927886.
Anurag Rai, Amit Saxena, Manish Manoria, “Cloud based Security Framework for Anomaly Based Intrusion Detection using Machine Learning Techniques,” International Journal of Engineering Research & Technology, (NCRIETS-2019 Conference Proceedings), vol. 7, no. 12, pp. 1-5, 2019.
SashoNedelkoski, Jorge Cardoso, and Odej Kao, “Anomaly detection and classification using distributed tracing and deep learning,” Proceedings of 19th IEEE/ACM International Symposium on Cluster, Cloud and Grid Computing (CCGRID-2019), pp. 241-250, 2019, DOI: 10.1109/CCGRID.2019.00038.
Hye-Young Kim, “A scheme of anomalous detection based on reinforcement learning for load balancing,” IOP Conf. Series: Materials Science and Engineering, vol. 790, no. 1, pp. 1-7, 2020, DOI: 10.1088/1757-899X/790/1/012035.
JeffreyCKimmel, MahmoudAbdelsalam, and MaanakGupta, “Analyzing machine learning approaches for online malware detection in cloud,” in Proceedings of 2021 IEEE International Conference on Smart Computing (SMARTCOMP), pp. 189-196, 2021, DOI: 10.1109/SMARTCOMP52413.2021.00046.
SangitaBaban Mule, MohiniDilipChikane, BankarArti Sunil, Sunil SudamKhatal, “Advanced and secure incursion detection system using auto-encoder and support vector machine in cloud computing: A Review,” International Journal of Advance Scientific Research & ET, vol. 4, no. 12, pp. 35-39, 2021
Kumar Pramanik, K. K., Neha, R. ., Limkar, S. ., Sule, B. ., Qureshi, A., & Kumar, K. S. . (2023). Accurate Classifier Based Face Recognition using Deep Learning Architectures by Noise Filtration with Classification. International Journal of Intelligent Systems and Applications in Engineering, 11(3s), 179–183. Retrieved from https://ijisae.org/index.php/IJISAE/article/view/2558
Zeeshan Ahmad, Adnan Shahid Khan, KashifNisar, IramHaider, Rosilah Hassan,Muhammad ReazulHaque, SeleviawatiTarmizi and Joel J. P. C. Rodrigues, “Anomaly detection using deep neural network for IoT architecture,” Applied Sciences, vol. 11, no. 15, pp. 1-19, 2021, DOI: 10.3390/app11157050.
Rayeesa Malik, Yashwant Singh, Zakir Ahmad Sheikh, Pooja Anand,Pradeep Kumar Singh, and TewabeChekoleWorkneh, “An improved deep belief network IDS on IoT-based network for traffic systems,” Journal of Advanced Transportation, vol. 2022, pp. 1-17, 2022, DOI: 10.1155/2022/7892130.
ShaokangCai, Dezhi Han, Xinming Yin, Dun Li and Chin-Chen Chang, “A Hybrid parallel deep learning model for efficient intrusion detection based on metric learning,” Connection Science, vol. 34, no. 1, pp. 551-577, 2022, DOI: 10.1080/09540091.2021.2024509.
Banavathu, Rajarao, and Sreenivasulu Meruva. "Efficient secure data storage based on novel blockchain model over IoT-based smart computing systems." Measurement: Sensors 27(2023):100741. DOI: https://doi.org/10.1016/j.measen.2023.100741
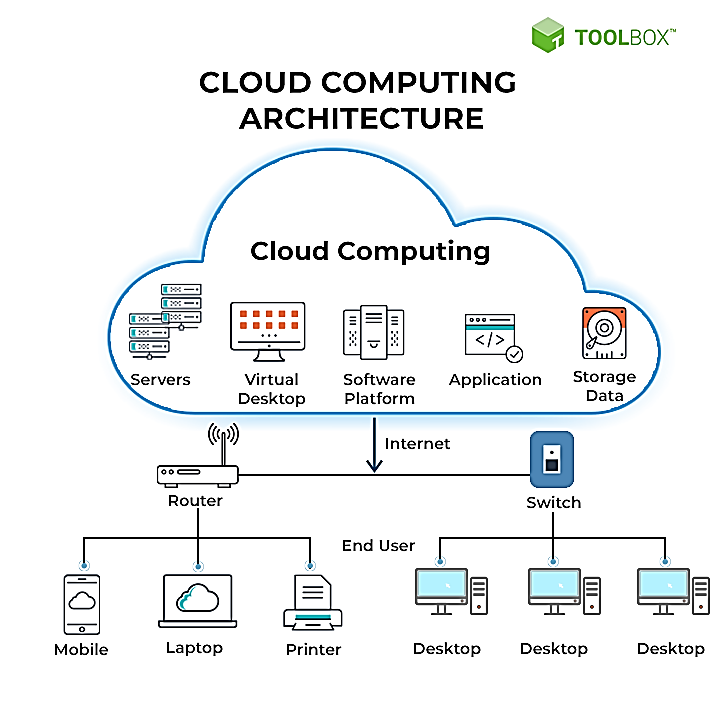
Cloud Architecture, Available online: https://pimages.toolbox.com/wp-content/uploads/2021/07/09134159/38-3.png
Kartika S. (2016). Analysis of “SystemC” design flow for FPGA implementation. International Journal of New Practices in Management and Engineering, 5(01), 01 - 07. Retrieved from http://ijnpme.org/index.php/IJNPME/article/view/41
Martin Duggan, The Application of Machine Learning to Optimise Live Migration in Cloud Data Centres, Ph.D., Thesis, 2019, DOI: 10.13140/RG.2.2.33506.27848
AbdulatifAlabdulatif, HeshanKumarage, Ibrahim Khalil, Xun Yi, Privacy-preserving anomaly detection in cloud with lightweight homomorphic encryption, Journal of Computer and System Sciences, vol. 90, p. 28-45,2017, DOI: https://doi.org/10.1016/j.jcss.2017.03.001