A Novel Method of Enhancing Security Solutions and Energy Efficiency of IoT Protocols
Main Article Content
Abstract
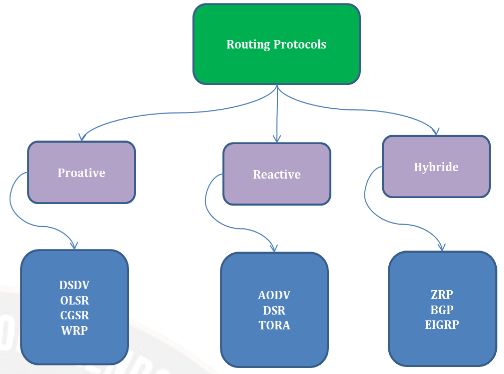
Mobile Ad-hoc Networks (MANET’s) are wireless networks that are capable of operating without any fixed infrastructure. MANET routing protocols must adhere to strict secrecy, integrity, availability and non-repudiation criteria. In MANETs, attacks are roughly categorised into two types: active and passive. An active attack attempts to modify or remove data being transferred across a network. On the other hand, passive attack does not modify or erase the data being sent over the network. The majority of routing protocols for MANETs were built with little regard for security and are therefore susceptible to a variety of assaults. Routing technologies such as AODV and dynamic source routing are quite common. Both however are susceptible to a variety of network layer attacks, including black holes, wormholes, rushing, byzantine, information disclosure. The mobility of the nodes and the open architecture in which the nodes are free to join or leave the network keep changing the topology of the network. The routing in such scenarios becomes a challenging task since it has to take into account the constraints of resources of mobile devices. In this an analysis of these protocols indicates that, though proactive routing protocols maintain a route to every destination and have low latency, they suffer from high routing overheads and inability to keep up with the dynamic topology in a large sized network. The reactive routing protocols in contrast have low routing overheads, better throughput and higher packet delivery ratio. AODVACO-PSO-DHKE Methodology boosts throughput by 10% while reducing routing overhead by 7%, latency by 8% and energy consumption by 5%. To avoid nodes always being on, a duty cycle procedure that's also paired with the hybrid method is used ACO-FDR PSO is applied to a 100-node network and NS-3 is used to measure various metrics such as throughput, latency, overhead, energy consumption and packet delivery ratio.
Article Details
References
. S Sarkar and R Datta, A Secure and Energy-efficient Stochastic Multipath Routing for Self-organized Mobile Ad Hoc Networks, Ad Hoc Networks, 37 (2019), 209-227.
. L Abusalah, A Khokhar, and Mohsen Guizani, A Survey of Secure Mobile Ad Hoc Routing Protocols, IEEE Communications Surveys & Tutorials, 10 (4) (2018), 78-93.
. M. Swathi Pai, M. Shruthi and B. Naveen K, "Internet of Things: A Survey on Devices, Ecosystem, Components and Communication Protocols," 2020 4th International Conference on Electronics, Communication and Aerospace Technology (ICECA), 2020, pp. 611-616, doi: 10.1109/ICECA49313.2020.9297458.
. S. B. Sridhara, K. B. Naveen, M. Ramesha, and G. N. Pai, “Internet of things: Internet revolution, impact, technology road map and features,” Adv. Math. Sci. J., vol. 9, no. 7, pp. 4405–4414, 2020, doi: 10.37418/amsj.9.7.11.
. C. Toh, H.Cobb and D. Scott. “Performance Evaluation of Battery-Life-Aware Routing Schemes for Wireless Ad Hoc Networks”, Proc. IEEE International Conference on Communication, Helsinki, Finland, pp.2824-2829, 2018.
. Shivashankar, and S. Mehta, “MANET topology for disaster management using wireless sensor network,” in International Conference on Communication and Signal Processing, ICCSP 2016, 2016, pp. 0736–0740, doi: 10.1109/ICCSP.2016.7754242
. Jayashri N, Veeresh Rampur, Durgaprasad Gangodkar, Abirami M, Balarengadurai C, Anil Kumar N, Improved block chain system for high secured IoT integrated supply chain, Measurement: Sensors, Volume 25, 2023, 100633.
. Rajashanthi, M. and Valarmathi, K.: A Secure Trusted Multipath Routing and Optimal Fuzzy Logic for Enhancing QoS in MANETs. Wireless Personal Communications, 112, 75-90 (2020).
. B.S., Ramesh Naidu, P., Sridhara, S.B. (2023). Internet of Things and Cognitive Radio Networks: Applications, Challenges and Future. In: Yadav, S., Chaudhary, K., Gahlot, A., Arya, Y., Dahiya, A., Garg, N. (eds) Recent Advances in Metrology . Lecture Notes in Electrical Engineering, vol 906. Springer, Singapore. https://doi.org/10.1007/978-981-19-2468-2_3.
. S. B. M, P. Pavankumar, N. K. Darwante, "Performance Monitoring and Dynamic Scaling Algorithm for Queue Based Internet of Things," 2022 International Conference on Innovative Computing, Intelligent Communication and Smart Electrical Systems (ICSES), 2022, pp. 1-7, doi: 10.1109/ICSES55317.2022.9914108.
. A. Singla, N. Sharma, "IoT Group Key Management using Incremental Gaussian Mixture Model," 2022 3rd International Conference on Electronics and Sustainable Communication Systems (ICESC), 2022, pp. 469-474, doi: 10.1109/ICESC54411.2022.9885644.
. S. Reddy P, P. S. Patwal, "Data Analytics and Cloud-Based Platform for Internet of Things Applications in Smart Cities," 2022 International Conference on Industry 4.0 Technology (I4Tech), 2022, pp. 1-6, doi: 10.1109/I4Tech55392.2022.9952780.
. A. Sharma, K. S and M. R. Arun, "Priority Queueing Model-Based IoT Middleware for Load Balancing," 2022 6th International Conference on Intelligent Computing and Control Systems (ICICCS), 2022, pp. 425-430, doi: 10.1109/ICICCS53718.2022.9788218.
. M. Nagabushanam, H. G. Govardhana Reddy & K. Raghavendra (2022) Vector space modelling-based intelligent binary image encryption for secure communication, Journal of Discrete Mathematical Sciences and Cryptography, 25:4, 1157-1171, DOI: 10.1080/09720529.2022.2075090.
. Pankaj Mudholkar, Megha Mudholkar, B S Puneeth Kumar and S. Srinivasulu Raju (2021), Smart Villages: IoT Technology Based Transformation, Journal of Physics: Conference Series, 2070(1), pp. 012128. https://doi.org/10.1088/1742-6596/2070/1/012128.
. Gurung, S., Chauhan, S.: A dynamic threshold based algorithm for improving security and performance of AODV under black-hole attack in MANET. Wireless Networks, 25(4), 1685-1695 (2019).
. Jacob, S.S., Hussain, N., Chennappan, R., Sakhare, D.T. (2023). Convergence of Communication Technologies with Internet of Things. In: Hemanth, J., Pelusi, D., Chen, J.IZ. (eds) Intelligent Cyber Physical Systems and Internet of Things. ICoICI 2022. Engineering Cyber-Physical Systems and Critical Infrastructures, vol 3. Springer, Cham. https://doi.org/10.1007/978-3-031-18497-0_48
. Rajeswari, A.R., Kulothungan, K., Ganapathy, S. and Kannan, A., 2019. A trusted fuzzy based stable and secure routing algorithm for effective communication in mobile adhoc networks. Peer-to-Peer Networking and Applications, 12(5), pp.1076-1096.
. Krishnan, R.S., Julie, E.G., Robinson, Y.H., Kumar, R., Son, L.H., Tuan, T.A. and Long, H.V., 2020. Modified zone based intrusion detection system for security enhancement in mobile ad hoc networks. Wireless Networks, 26(2), pp.1275-1289.
. Bisen, D. and Sharma, S., 2018. An enhanced performance through agent-based secure approach for mobile ad hoc networks. International Journal of Electronics, 105(1), pp.116-136.
. Vatambeti, R., Sanshi, S. and Krishna, D.P., 2021. An efficient clustering approach for optimized path selection and route maintenance in mobile ad hoc networks. Journal of Ambient Intelligence and Humanized Computing, pp.1-15.
. Vatambeti, R., 2020. A novel wolf based trust accumulation approach for preventing the malicious activities in mobile ad hoc network. Wireless Personal Communications, 113(4), pp.2141-2166.
. Xu, H., Si, H., Zhang, H., Zhang, L., Leng, Y., Wang, J. and Li, D., 2020. Trust-based probabilistic broadcast scheme for mobile ad hoc networks. IEEE Access, 8, pp.21380-21392.