An Implementing A Continuous Authentication Protocol To Improve Robustness Security Threats On IoT Using ESP8266
Main Article Content
Abstract
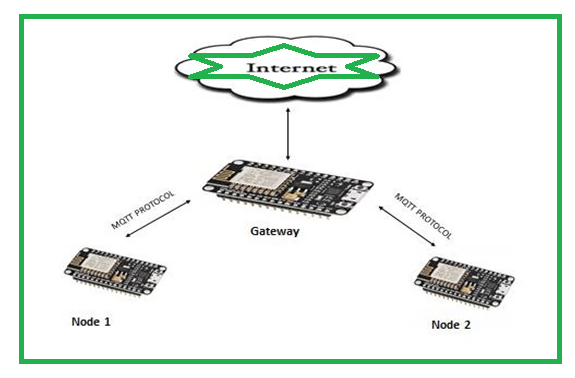
The Internet of Things (IoT) is a network of physical things that are outfitted with sensors, software, and other technologies that are able to communicate and exchange data with other devices and systems over the Internet. Because of the diversity of their surroundings, IoT systems are sensitive to network attacks. The IoT could be the source of these dangers and attacks. There are a lot of devices that communicate with each other via the IoT, and one of the most critical components of this is to maintain IoT security. IoT devices are a prime target for attackers and pose a serious risk of impersonation during a call. Proposals to prevent session hijacking in device-to-device communication are made in this research study. User-to-device authentication relies on usernames and passwords, but continuous authentication doesn't. This protocol relies on device features and contextual information. Moreover, this protocol reduces the synchronization losses using shadow IDs and emergency key. In addition, the protocol’s robustness will be tested by providing security and performance analysis.
Article Details
References
Alladi T, Chamola V. HARCI: A two-way authentication protocol for three entity healthcare IoT networks. IEEE Journal on Selected Areas in Communications. 2020 Sep 1;39(2):361-9.
Alladi T, Chamola V, Kumar N. PARTH: A two-stage lightweight mutual authentication protocol for UAV surveillance networks. Computer Communications. 2020 Jul 1;160:81-90.
Bhaskaran, R., Ramamoorthy, K., Fancy, C., Jayasankar, T.(2022), “Replica Node Detection using Metaheuristic Algorithms in Wireless Sensor Networks”, International Journal of Engineering Trends and Technology, 70(5), 339-345
Awan KA, Ud Din I, Almogren A, Almajed H. AgriTrust—a trust management approach for smart agriculture in cloud-based internet of agriculture things. Sensors. 2020 Oct 29;20(21):6174.
Sowah RA, Boahene DE, Owoh DC, Addo R, Mills GA, Owusu-Banahene W, Buah G, Sarkodie-Mensah B. Design of a secure wireless home automation system with an open home automation bus (OpenHAB 2) framework. Journal of Sensors. 2020 Oct 30;2020.
Jaya NI, Hossain MF. A prototype air flow control system for home automation using mqtt over websocket in aws iot core. In2018 International Conference on Cyber-Enabled Distributed Computing and Knowledge Discovery (CyberC) 2018 Oct 18 (pp. 111-1116). IEEE.
J. V. Anchitaalagammai, T. Jayasankar, P. Selvaraj, Mohamed Yacin Sikkandar, M. Zakarya, Mohamed Elhoseny and K. Shankar, “Energy Efficient Cluster-Based Optimal Resource Management in IoT Environment”, Computers, Materials & Continua, vol. 70, no.1, pp. 1248-1261, 2022, ISSN: 1752-1767 (Print) 1546-2226.
Hayashi V, Ruggiero W. Non-invasive challenge response authentication for voice transactions with smart home behavior. Sensors. 2020 Nov 17;20(22):6563.
Faid A, Sadik M, Sabir E. An agile AI and IoT-augmented smart farming: a cost-effective cognitive weather station. Agriculture. 2021 Dec 29;12(1):35.
Hasan D, Ismaeel A. Designing ECG monitoring healthcare system based on internet of things blynk application. Journal of applied science and technology trends. 2020 Jul 31;1(3):106-11.
M. L. Das, A. Saxena, and V. P. Gulati. A dynamic id-based remote user authentication scheme. IEEE Transactions on Consumer Electronics, 50(2):629–631, May 2004.
. L. Das, A. Saxena, and V. P. Gulati. A dynamic id-based remote user authentication scheme. IEEE Transactions on Consumer Electronics, 50(2):629–631, May 2004
Y.-F. Chang, W.-L. Tai, and H.-C. Chang. Untraceable dynamicidentity-based remote user authentication scheme with verifiable pass word update. International Journal of Communication Systems, 27(11):3430–3440, 2014
S. Sarma, S. Weis, and D. Engles. Radio frequency identification: Security risks and challenges. Cryptobytes, 6(1):2–9, 2003.
D. Molnar, A. Soppera, and D. Wagner. A scalable, delegatable pseudonym protocol enabling ownership transfer of rfid tags. Proc. Workshop on Selected Areas in Cyptography, LNCS Springer, SAC2005,3897, 2006.
Ruels, R. L. Rivest, and M. Szudlo. The blocker tag : selective blocking of rfid tags for consumer privacy. The 8th ACM Conference on Computer and Communications Security, pages 103–111, 2003.
S. A. Weis, S. E. Sarma, R. L. Rivest, and D. W. Engels. Security and privacy aspects of low-cost radio frequency identification systems. In Security in pervasive computing, pages 201–212. Springer, 2004.
Juels. Rfid security and privacy: A research survey. Selected Areas in Communications, IEEE Journal on, 24(2):381–394, 2006.
P. Peris-Lopez, T.-L. Lim, and T. Li. Providing stronger authentication at a low cost to rfid tags operating under the epcglobal framework. In Embedded and Ubiquitous Computing, 2008. EUC’08. IEEE/IFIP International Conference on, volume 2, pages 159–166. IEEE, 2008.D. M. Konidala and K. Kim. Rfid tag-reader mutual authentication scheme utilizing tags access password. Auto-ID Labs White Paper WP- HARDWARE-033, 2007.
Louis Jestin, & Ibrahim Hamdan. (2022). Architecture Modelling of MOS Device for the Circuit simulation. Acta Energetica, (02), 21–27. Retrieved from http://actaenergetica.org/index.php/journal/article/view/465
T.-L. Lim and T. Li. Addressing the weakness in a lightweight rfid tag-reader mutual authentication scheme. In Global Telecommunications Conference, 2007. GLOBECOM’07. IEEE, pages 59–63. IEEE, 2007.
C.-L. Chen and Y.-Y. Deng. Conformation of epc class 1 generation 2 standards rfid system with mutual authentication and privacy pro- tection. Engineering Applications of Artificial Intelligence, 22(8):1284– 1291, 2009.
Jakub Siemek, & Dr. Prakash Pise. (2022). Model Designing of Analog Integrated Circuits for the Physiological Signals. Acta Energetica, (03), 01–08. Retrieved from http://actaenergetica.org/index.php/journal/article/view/470
P. Peris-Lopez, J. C. Hernandez-Castro, J. M. Tapiador, and J. C. Van der Lubbe. Cryptanalysis of an epc class-1 generation-2 standard compliant authentication protocol. Engineering Applications of Artificial Intelligence, 24(6):1061–1069, 2011.
Vibha Yadav, Manas Kumar Mishra, Singh, AK & Gore, MM 2009, ‘Localization Scheme for Three Dimensional Wireless Sensor Networks using GPS enabled Mobile Sensor Nodes’, International Journal of Next-Generation Networks (IJNGN),vol. 1, no.1,pp. 60-72.
Hongyang Chen, Qingjiang Shi, Pei Huang, Vincent Poor, H & Kaoru Sezaki 2009, ‘Mobile Anchor Assisted Node Localization for Wireless Sensor Networks’, IEEE 20th International Symposium on Personal, Indoor and Mobile Radio Communications, Tokyo,Japan, pp.87-91