A State-of-the-Art Survey for IoT Security and Energy Management based on Hashing Algorithms
Main Article Content
Abstract
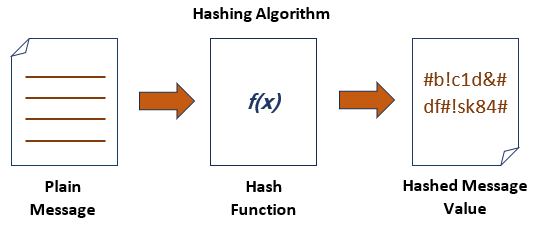
The Internet of Things (IoT) has developed as a disruptive technology with wide-ranging applications across several sectors, enabling the connecting of devices and the acquisition of substantial volumes of data. Nevertheless, the rapid expansion of networked gadgets has generated substantial apprehensions pertaining to security and energy administration. This survey paper offers a detailed examination of the present state of research and advancements in the field of Internet of Things (IoT) security and energy management. The work places special emphasis on the use of hashing algorithms in this context. The security of the Internet of Things (IoT) is a crucial element in safeguarding the confidentiality, integrity, and availability of data inside IoT environments. Hashing algorithms have gained prominence as a fundamental tool for enhancing IoT security. This survey reviews the state of the art in cryptographic hashing techniques and their application in securing IoT devices, data, and communication. Furthermore, the efficient management of energy resources is essential to prolong the operational lifespan of IoT devices and reduce their environmental impact. Hashing algorithms are also instrumental in optimizing energy consumption through data compression, encryption, and authentication. This survey explores the latest advancements in energy-efficient IoT systems and how hashing algorithms contribute to energy management strategies. Through a comprehensive analysis of recent research findings and technological advancements, this survey identifies key challenges and open research questions in the fields of IoT security and energy management based on hashing algorithms. It provides valuable insights for researchers, practitioners, and policymakers to further advance the state of the art in these critical IoT domains.
Article Details
References
H. Kopetz and W. Steiner, "Internet of things," in Real-time systems: design principles for distributed embedded applications: Springer, 2022, pp. 325-341.
M. Rupesh and N. A. Selvan, "Design of IoT based smart energy meter for home appliances," in Journal of Physics: Conference Series, 2021, vol. 1964, no. 5: IOP Publishing, p. 052001.
A. Rekeraho, D. T. Cotfas, P. A. Cotfas, T. C. B?lan, E. Tuyishime, and R. Acheampong, "Cybersecurity challenges in IoT-based smart renewable energy," 2023.
Sami, Teba Mohammed Ghazi, Subhi RM Zeebaree, and Sarkar Hasan Ahmed. "A Comprehensive Review of Hashing Algorithm Optimization for IoT Devices." International Journal of Intelligent Systems and Applications in Engineering 11.6s (2023): 205-231.
R. C. Motta, K. M. de Oliveira, and G. H. Travassos, "An evidence-based roadmap for IoT software systems engineering," Journal of Systems and Software, vol. 201, p. 111680, 2023.
Sadeeq, Mohammed AM, et al. "Internet of Things security: a survey." 2018 International Conference on Advanced Science and Engineering (ICOASE). IEEE, 2018.
Ageed, Zainab Salih, et al. "A state of art survey for intelligent energy monitoring systems." Asian Journal of Research in Computer Science 8.1 (2021): 46-61.
J. C. M'Kaila and L. Rajabion, "A Strategic Approach to IoT Security by Working Towards a Secure IoT Future," International Journal of Hyperconnectivity and the Internet of Things (IJHIoT), vol. 7, no. 1, pp. 1-18, 2023.
A. R. Kairaldeen, N. F. Abdullah, A. Abu-Samah, and R. Nordin, "Data integrity time optimization of a blockchain IoT smart home network using different consensus and hash algorithms," Wireless Communications and Mobile Computing, vol. 2021, pp. 1-23, 2021.
J. Jebrane and S. Lazaar, "A performance comparison of lightweight cryptographic algorithms suitable for IoT transmissions," General Letters in Mathematics (GLM), vol. 10, no. 2, 2021.
N. A. M. Alhammadi and K. H. Zaboon, "A review of IoT applications, attacks and its recent defense methods," Journal of Global Scientific Research, vol. 7, no. 3, pp. 2128-2134, 2022.
Sadeeq, Mohammed Mohammed, et al. "IoT and Cloud computing issues, challenges and opportunities: A review." Qubahan Academic Journal 1.2 (2021): 1-7.
K. Janani and S. Ramamoorthy, "IoT security and privacy using deep learning model: a review," in 2021 International conference on intelligent technologies (CONIT), 2021: IEEE, pp. 1-6.
N. Lata and R. Kumar, "Security in internet of things (IoT): challenges and models," Mathematical Statistician and Engineering Applications, vol. 71, no. 2, pp. 75–81-75–81, 2022.
E. Leloglu, "A review of security concerns in Internet of Things," Journal of Computer and Communications, vol. 5, no. 1, pp. 121-136, 2016.
A. H. Bagdadee, L. Zhang, and M. Saddam Hossain Remus, "A brief review of the IoT-based energy management system in the smart industry," Artificial Intelligence and Evolutionary Computations in Engineering Systems, pp. 443-459, 2020.
Rashid, Zryan N., et al. "Distributed and Parallel Computing System Using Single-Client Multi-Hash Multi-Server Multi-Thread." 2021 1st Babylon International Conference on Information Technology and Science (BICITS). IEEE, 2021.
T. V. K. Nguyen, "From theory to practice: towards scalable and smart energy monitoring based on the Internet of Things," Macquarie University, 2023.
S. Benhamaid, A. Bouabdallah, and H. Lakhlef, "Recent advances in energy management for Green-IoT: An up-to-date and comprehensive survey," Journal of Network and Computer Applications, vol. 198, p. 103257, 2022.
A.-R. Al-Ali, I. A. Zualkernan, M. Rashid, R. Gupta, and M. AliKarar, "A smart home energy management system using IoT and big data analytics approach," IEEE Transactions on Consumer Electronics, vol. 63, no. 4, pp. 426-434, 2017.
L. V. Cherckesova, O. A. Safaryan, N. G. Lyashenko, and D. A. Korochentsev, "Developing a New Collision-Resistant Hashing Algorithm," Mathematics, vol. 10, no. 15, p. 2769, 2022.
Sadeeq, Mohammed AM, and Subhi Zeebaree. "Energy management for internet of things via distributed systems." Journal of Applied Science and Technology Trends 2.02 (2021): 59-71.
P. P. Pittalia, "A comparative study of hash algorithms in cryptography," International Journal of Computer Science and Mobile Computing, vol. 8, no. 6, pp. 147-152, 2019.
A. Sideris, T. Sanida, and M. Dasygenis, "Hardware acceleration of SHA-256 algorithm using NIOS-II processor," in 2019 8th International Conference on Modern Circuits and Systems Technologies (MOCAST), 2019: IEEE, pp. 1-4.
Sami, Teba Mohammed Ghazi, Subhi RM Zeebaree, and Sarkar Hasan Ahmed. "A Novel Multi-Level Hashing Algorithm to Enhance Internet of Things Devices’ and Networks’ Security." International Journal of Intelligent Systems and Applications in Engineering 12.1s (2024): 676-696.
B. U. I. Khan, R. F. Olanrewaju, M. A. Morshidi, R. N. Mir, M. L. B. M. Kiah, and A. M. Khan, "Evolution and analysis of secured hash algorithm (SHA) family," Malaysian Journal of Computer Science, vol. 35, no. 3, pp. 179-200, 2022.
X. Zhang and H. Hu, "Optimization of hash function implementation for bitcoin mining," in 3rd International Conference on Mechatronics Engineering and Information Technology (ICMEIT 2019), 2019: Atlantis Press, pp. 448-452.
E. V. Maliberan, "Modified SHA1: a hashing solution to secure web applications through login authentication," International Journal of Communication Networks and Information Security, vol. 11, no. 1, pp. 36-41, 2019.
D. M. A. Cortez, A. M. Sison, and R. P. Medina, "Cryptanalysis of the Modified SHA256," in Proceedings of the 2020 4th High Performance Computing and Cluster Technologies Conference & 2020 3rd International Conference on Big Data and Artificial Intelligence, 2020, pp. 179-183.
R. Martino and A. Cilardo, "Designing a SHA-256 processor for blockchain-based IoT applications," Internet of Things, vol. 11, p. 100254, 2020.
H. L. Pham, T. H. Tran, T. D. Phan, V. T. D. Le, D. K. Lam, and Y. Nakashima, "Double SHA-256 hardware architecture with compact message expander for bitcoin mining," IEEE Access, vol. 8, pp. 139634-139646, 2020.
A. Smolarz et al., "Using hash functions to protect critical messages from changes in risky computing systems," in CITRisk, 2021, pp. 434-444.
P. J. F. Bemida, A. M. Sison, and R. P. Medina, "Modified SHA-512 Algorithm for Secured Password Hashing," in 2021 Innovations in Power and Advanced Computing Technologies (i-PACT), 2021: IEEE, pp. 1-9.
T. F. G. Q. Rogel LadiaQuilala, "Document verification using quick response code with modified secure hash algorithm-1 and modified blowfish algorithm," Indonesian Journal of Electrical Engineering and Computer Science, vol. 28, pp. 470-479, 2022, doi: 10.11591/ijeecs.v28.i1.
H. L. Pham, T. H. Tran, V. T. D. Le, and Y. Nakashima, "A high-efficiency FPGA-based multimode SHA-2 accelerator," IEEE Access, vol. 10, pp. 11830-11845, 2022.
M. D. Mohanty et al., "Design of Smart and Secured Healthcare Service Using Deep Learning with Modified SHA-256 Algorithm," in Healthcare, 2022, vol. 10, no. 7: MDPI, p. 1275.
S. Suhaili and N. Julai, "FPGA-based Implementation of SHA-256 with Improvement of Throughput using Unfolding Transformation," Pertanika Journal of Science & Technology, vol. 30, no. 1, 2022.
G. Uganya and R. Baskar, "Modified Elliptic Curve Cryptography Multi-Signature Scheme to Enhance Security in Cryptocurrency," Computer Systems Science & Engineering, vol. 45, no. 1, 2023.