Security Privacy Process Involvement in Cloud Security for Data Preservation against Data Malicious Activity
Main Article Content
Abstract
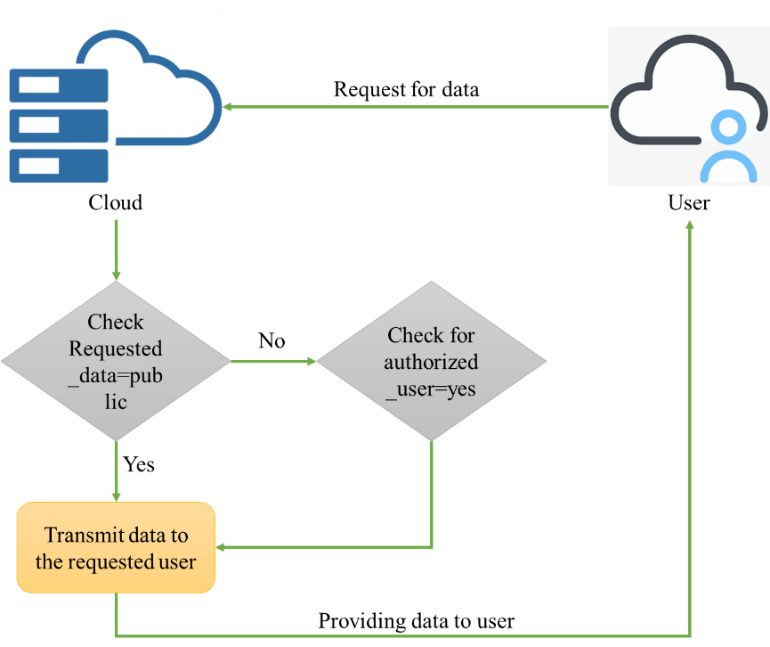
Cloud data sent from the person is attacked, leading to data hacking. Data classification can be made by malware detection, leading to the data warehouse technique and data storage. The cloud data from a particular internet protocol address cannot be hacked. Only random cloud data is hacked. Even though this leads to some illegal issues. The method of managing the cloud data and maintaining the factor to hack illegal cloud data has been proposed. The method of malware detection and ML-based end-to-end malware detection are used in calculating the time efficiency. The malware detection and defence method has been introduced for managing the data tracking and the system's formation to hack unwanted data. The time efficiency calculation for the data transmitted in the network has been enabled for the cloud data sent and received. The data from each router makes the data store 12% of the unwanted compared to the original messages. The factor for managing the individual aspect to produce the data is 30% of the database. This will contain 20% of the data in formulating the cloud storage system, which makes the data classifications. 4% of redundant data from the database has been enveloped for the data classifications. Meanwhile, the data attack can be evaluated using the malware detector and also manages classification method for evaluation of data and formation of the system to produce data from the appearance of Secure data clouds.