An Event Based Digital Forensic Scheme for Vehicular Networks
Main Article Content
Abstract
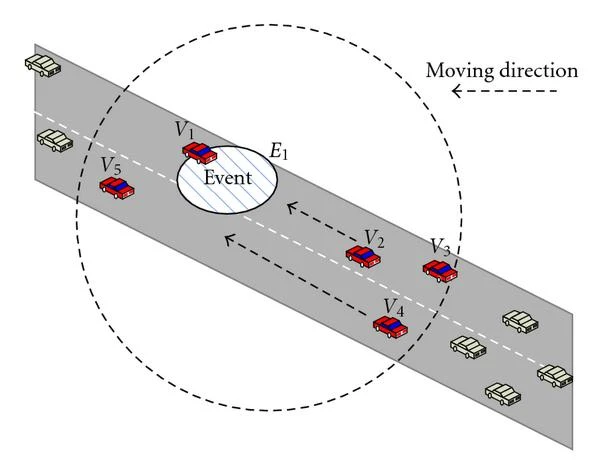
The software in today's cars has become increasingly important in recent years. The development of high-tech driver assistance devices has helped fuel this movement. This tendency is anticipated to accelerate with the advent of completely autonomous vehicles. As more modern vehicles incorporate software and security-based solutions, "Event-Based digital forensics," the analysis of digital evidence of accidents and warranty claims, has become increasingly significant. The objective of this study is to ascertain, in a realistic setting, whether or not digital forensics can be successfully applied to a state-of-the-art automobile. We did this by dissecting the procedure of automotive forensics, which is used on in-car systems to track the mysterious activity by means of digital evidence. We did this by applying established methods of digital forensics to a state-of-the-art car.
Our research employs specialized cameras installed in the study areas and a log of system activity that may be utilized as future digital proof to examine the effectiveness of security checkpoints and other similar technologies. The goal is to keep an eye on the vehicles entering the checkpoint, look into them if there is any reason to suspect anything, and then take the appropriate measures. The problem with analyzing this data is that it is becoming increasingly complex and time-consuming as the amount of data that has been collected keeps growing. In this paper, we outline a high-level methodology for automotive forensics to fill in the blanks, and we put it through its paces on a network simulator in a state-of-the-art vehicle to simulate a scenario in which devices are tampered with while the car is in motion. Here, we test how well the strategy functions. Diagnostics over IP (Diagnostics over IP), on-board diagnostics interface, and unified diagnostic services are all used during implementation. To work, our solution requires vehicles to be able to exchange diagnostic information wirelessly.
These results show that it is possible to undertake automotive forensic analysis on state-of-the-art vehicles without using intrusion detection systems or event data recorders, and they lead the way towards a more fruitful future for automotive forensics. The results also show that modern autos are amenable to forensic automotive analysis.
Article Details
References
M. Poongodi, V. Vijayakumar, F. Al-Turjman, M. Hamdi and M. Ma, "Intrusion Prevention System for DDoS Attack on VANET With reCAPTCHA Controller Using Information Based Metrics," IEEE Access, vol. 7, pp. 158481-158491, 2019.
A. R. Gad, A. A. Nashat and T. M. Barkat, "Intrusion Detection System Using Machine Learning for Vehicular Ad Hoc Networks Based on ToN-IoT Dataset," IEEE Access, vol. 9, pp. 142206-142217, 2021.
M. Poongodi, M. Hamdi, A. Sharma, M. Ma, and P. K. Singh, "DDoS Detection Mechanism Using Trust-Based Evaluation System in VANET," IEEE Access, vol. 7, pp. 183532-183544, 2019.
Junwei Liang, Jianyong Chen, Yingying Zhu and Richard Yu,"A novel Intrusion Detection System for Vehicular Ad Hoc Networks (VANETs) based on differences of traffic flow and position,"Applied Soft Computing, Vol. 75, pp. 712-727, February 2019.
Erfan A.Shams, Ahmet Rizaner, Ali Hakan Ulusoy,"Trust aware support vector machine intrusion detection and prevention system in vehicular ad hoc networks,"Computers & Security, Vol. 78, pp. 245-254, September 2018.
Neeraj Kumar and Naveen Chilamkurti, "Collaborative trust aware intelligent intrusion detection in VANETs,"Computers & Electrical Engineering, Vol. 40, Issue 6, pp. 1981-1996, August 2014.
P. Remya krishnan and P. Arun Raj Kumar, "Detection and Mitigation of Smart Blackhole and Gray Hole Attacks in VANET Using Dynamic Time Warping," Wireless Personal Communications, 2021.
S. Prabakeran and T. Sethukarasi,"Optimal solution for malicious node detection and prevention using hybrid chaotic particle dragonfly swarm algorithm in VANETs,"Wireless Networks, vol. 26, pp. 5897–5917, 2020.
L. Wang, J. Yang, M. Workman and P. Wan, "Effective algorithms to detect stepping-stone intrusion by removing outliers of packet RTTs," Tsinghua Science and Technology, vol. 27, no. 2, pp. 432-442, April 2022.
D. Pan, J. Yuan, L. Li and D. Sheng, "Deep neural network-based classification model for Sentiment Analysis," 2019 6th International Conference on Behavioral, Economic and Socio-Cultural Computing (BESC), pp. 1-4, 2019.
W. Zhong, N. Yu and C. Ai, "Applying big data-based deep learning system to intrusion detection," Big Data Mining and Analytics, vol. 3, no. 3, pp. 181-195, Sept. 2020.
Y. Miao, Y. Tang, B. A. Alzahrani, A. Barnawi, T. Alafif and L. Hu, "Airborne LiDAR Assisted Obstacle Recognition and Intrusion Detection Towards Unmanned Aerial Vehicle: Architecture, Modeling and Evaluation," IEEE Transactions on Intelligent Transportation Systems, vol. 22, no. 7, pp. 4531-4540, July 2021.
M. A. Siddiqi and W. Pak, "An Agile Approach to Identify Single and Hybrid Normalization for Enhancing Machine Learning-Based Network Intrusion Detection," IEEE Access, vol. 9, pp. 137494-137513, 2021.
G. Pu, L. Wang, J. Shen and F. Dong, "A hybrid unsupervised clustering-based anomaly detection method," Tsinghua Science and Technology, vol. 26, no. 2, pp. 146-153, April 2021.
K. A. Garcia, R. Monroy, L. A. Trejo, C. Mex-Perera and E. Aguirre, "Analyzing Log Files for Postmortem Intrusion Detection," in IEEE Transactions on Systems, Man, and Cybernetics, Part C (Applications and Reviews), vol. 42, no. 6, pp. 1690-1704, Nov. 2012.
J. Zhang, M. Zulkernine and A. Haque, "Random-Forests-Based Network Intrusion Detection Systems," in IEEE Transactions on Systems, Man, and Cybernetics, Part C (Applications and Reviews), vol. 38, no. 5, pp. 649-659, Sept. 2008.
Y. Lin, Y. Gao, B. Li and W. Dong, "Revisiting Indoor Intrusion Detection With WiFi Signals: Do Not Panic Over a Pet!," in IEEE Internet of Things Journal, vol. 7, no. 10, pp. 10437-10449, Oct. 2020.
J. Yang, X. Chen, S. Chen, X. Jiang and X. Tan, "Conditional Variational Auto-Encoder and Extreme Value Theory Aided Two-Stage Learning Approach for Intelligent Fine-Grained Known/Unknown Intrusion Detection," in IEEE Transactions on Information Forensics and Security, vol. 16, pp. 3538-3553, 2021.
H. Yang and F. Wang, "Wireless Network Intrusion Detection Based on Improved Convolutional Neural Network," in IEEE Access, vol. 7, pp. 64366-64374, 2019.
J. Wang, Z. Tian, M. Zhou, J. Wang, X. Yang and X. Liu, "Leveraging Hypothesis Testing for CSI Based Passive Human Intrusion Direction Detection," in IEEE Transactions on Vehicular Technology, vol. 70, no. 8, pp. 7749-7763, Aug. 2021.
H. Sedjelmaci, S. M. Senouci and N. Ansari, "Intrusion Detection and Ejection Framework Against Lethal Attacks in UAV-Aided Networks: A Bayesian Game-Theoretic Methodology," in IEEE Transactions on Intelligent Transportation Systems, vol. 18, no. 5, pp. 1143-1153, May 2017.
S. Otoum, B. Kantarci and H. T. Mouftah, "On the Feasibility of Deep Learning in Sensor Network Intrusion Detection," in IEEE Networking Letters, vol. 1, no. 2, pp. 68-71, June 2019.