Outlier Detection Mechanism for Ensuring Availability in Wireless Mobile Networks Anomaly Detection
Main Article Content
Abstract
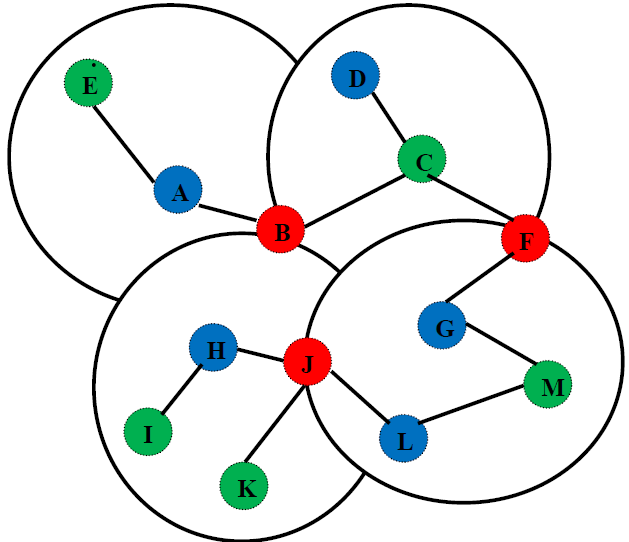
Finding things that are significantly different from, incomparable with, and inconsistent with the majority of data in many domains is the focus of the important research problem of anomaly detection. A noteworthy research problem has recently been illuminated by the explosion of data that has been gathered. This offers brand-new opportunities as well as difficulties for anomaly detection research. The analysis and monitoring of data connected to network traffic, weblogs, medical domains, financial transactions, transportation domains, and many more are just a few of the areas in which anomaly detection is useful. An important part of assessing the effectiveness of mobile ad hoc networks (MANET) is anomaly detection. Due to difficulties in the associated protocols, MANET has become a popular study topic in recent years. No matter where they are geographically located, users can connect to a dynamic infrastructure using MANETs. Small, powerful, and affordable devices enable MANETs to self-organize and expand quickly. By an outlier detection approach, the proposed work provides cryptographic property and availability for an RFID-WSN integrated network with node counts ranging from 500 to 5000. The detection ratio and anomaly scores are used to measure the system's resistance to outliers. The suggested method uses anomaly scores to identify outliers and provide defence against DoS attacks. The suggested method uses anomaly scores to identify outliers and provide protection from DoS attacks. The proposed method has been shown to detect intruders in a matter of milliseconds without interfering with authorised users' privileges. Throughput is improved by at least 6.8% using the suggested protocol, while Packet Delivery Ratio (PDR) is improved by at least 9.2% and by as much as 21.5%.
Article Details
References
M. Marimuthu and I. Krishnamurthi, “Enhanced OLSR for defense against DOS attack in ad hoc networks,” J. Commun. Networks, vol. 15, no. 1, pp. 31–37, Feb. 2013.
S. S. Rajput and M. C. Trivedi, “Securing zone routing protocol in MANET using authentication technique,” Proc. - 2014 6th Int. Conf. Comput. Intell. Commun. Networks, CICN 2014, pp. 872–877, 2014.
S. A. Selvi and A. Vijayaraj, “Increasing quality of service in video traffic using zone routing protocol in wireless networks,” in 2016 World Conference on Futuristic Trends in Research and Innovation for Social Welfare (Startup Conclave), 2016, pp. 1–5.
Chettri L., Bera R. A Comprehensive Survey on Internet of Things (IoT) Toward 5G Wireless Systems. IEEE Internet Things J. 2020;7:16–32. doi: 10.1109/JIOT.2019.2948888.
Andrews J.G., Buzzi S., Choi W., Hanly S.V., Lozano A., Soong A.C.K., Zhang J.C. What Will 5G Be? IEEE J. Sel. Areas Commun. 2014; 32:1065–1082. doi: 10.1109/JSAC.2014.2328098.
Imran A., Zoha A., Abu-Dayya A. Challenges in 5G: How to empower SON with big data for enabling 5G. IEEE Netw. 2014; 28:27–33. doi: 10.1109/MNET.2014.6963801.
Valastro G.C., Panno D., Riolo S. A SDN/NFV based C-RAN architecture for 5G Mobile Networks; Proceedings of the 2018 International Conference on Selected Topics in Mobile and Wireless Networking (MoWNeT); Tangier, Morocco. 20–22 June 2018; pp. 1–8.
Asghar A., Farooq H., Imran A. Self-Healing in Emerging Cellular Networks: Review, Challenges, and Research Directions. IEEE Commun. Tutor. 2018; 20:1682–1709. doi: 10.1109/COMST.2018.2825786.
Li R., Zhao Z., Zhou X., Ding G., Chen Y., Wang Z., Zhang H. Intelligent 5G: When Cellular Networks Meet Artificial Intelligence. IEEE Wirel. Commun. 2017; 24:175–183. doi: 10.1109/MWC.2017.1600304WC.
Wu J., Lee P.P.C., Li Q., Pan L., Zhang J. CellPAD: Detecting Performance Anomalies in Cellular Networks via Regression Analysis; Proceedings of the 2018 IFIP Networking Conference (IFIP Networking) and Workshops; Zurich, Switzerland. 14–16 May 2018; pp. 1–9.
Wang M., Handurukande S. A Streaming Data Anomaly Detection Analytic Engine for Mobile Network Management; Proceedings of the 2016 Intl IEEE Conferences on Ubiquitous Intelligence Computing, Advanced and Trusted Computing, Scalable Computing and Communications, Cloud and Big Data Computing, Internet of People, and Smart World Congress; Toulouse, France. 18–21 July 2016; pp. 722–729.
Song R., Liu F. Real-time anomaly traffic monitoring based on dynamic k-NN cumulative-distance abnormal detection algorithm; Proceedings of the 2014 IEEE 3rd International Conference on Cloud Computing and Intelligence Systems; Shenzhen, China. 27–29 November 2014; pp. 187–192.
Muñoz P., Barco R., Serrano I., Gómez-Andrades A. Correlation-Based Time-Series Analysis for Cell Degradation Detection in SON. IEEE Commun. Lett. 2016; 20:396–399. doi: 10.1109/LCOMM.2016.2516004.
Ibidunmoye O., Rezaie A., Elmroth E. Adaptive Anomaly Detection in Performance Metric Streams. IEEE Trans. Netw. Serv. Manag. 2018; 15:217–231. doi: 10.1109/TNSM.2017.2750906.
Alam M.R., Gerostathopoulos I., Prehofer C., Attanasi A., Bures T. A Framework for Tunable Anomaly Detection; Proceedings of the 2019 IEEE International Conference on Software Architecture (ICSA); Hamburg, Germany. 25–29 March 2019; pp. 201–210.
Hussain B., Du Q., Zhang S., Imran A., Imran M.A. Mobile Edge Computing-Based Data-Driven Deep Learning Framework for Anomaly Detection. IEEE Access. 2019; 7: 137656–137667. doi: 10.1109/ACCESS.2019.2942485.
Qin X., Tang S., Chen X., Miao D., Wei G. SQoE KQIs anomaly detection in cellular networks: Fast online detection framework with Hourglass clustering. China Commun. 2018; 15:25–37. doi: 10.1109/CC.2018.8485466.
Hussain B., Du Q., Ren P. Semi-supervised learning based big data-driven anomaly detection in mobile wireless networks. China Commun. 2018; 15:41–57. doi: 10.1109/CC.2018.8357700.
Akhi, A. B., Kanon, E. J., Kabir, A., &Banu, A. (2019).Network Intrusion Classification Employing Machine Learning: A Survey. (Doctoral dissertation)Department of Computer Science and Engineering, United International University, Bangladesh.
Alizadeh, H., Khoshrou, A., &Zuquete, A. (2015). Traffic classification and verification using unsupervised learning of Gaussian Mixture Models. In2015 IEEE international workshop on measurements & networking (M&N). 1-6. IEEE.
Amangele, P., Reed, M. J., Al-Naday, M., Thomos, N., & Nowak, M. (2019). Hierarchical Machine Learning for IoT Anomaly Detection in SDN. In2019 International Conference on Information Technologies (InfoTech). 1-4. IEEE.
Ashfaq, R. A. R., Wang, X. Z., Huang, J. Z., Abbas, H., & He, Y. L. (2017). Fuzziness based semisupervised learning approach for intrusion detection system.Information Sciences, 378, 484-497.
Aung, Y. Y., & Min, M. M (2018). An analysis of K-means algorithm based network intrusion detection system. Advances in Science, Technology and Engineering Systems Journal, 3(1), 496-501.
Bauer, F. C., Muir, D. R., &Indiveri, G (2019). Real-Time Ultra-Low Power ECG Anomaly Detection Using an Event-Driven Neuromorphic Processor. IEEE Transactions on Biomedical Circuits and Systems, 13, 1575–82. 2019.2953001
Bhati, B. S., Rai, C. S., Balamurugan, B., & Al-Turjman, F. (2020). An intrusion detection scheme based on the ensemble of discriminant classifiers.Computers & Electrical Engineering, 86, 106742.