Encryption and Decryption of Images with Pixel Data Modification Using Hand Gesture Passcodes
Main Article Content
Abstract
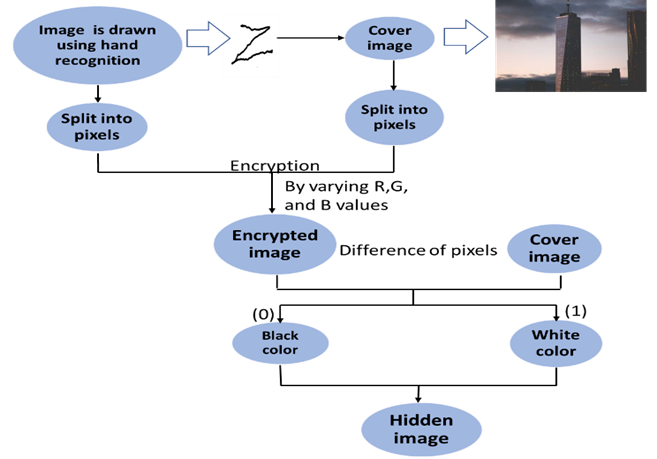
To ensure data security and safeguard sensitive information in society, image encryption and decryption as well as pixel data modifications, are essential. To avoid misuse and preserve trust in our digital environment, it is crucial to use these technologies responsibly and ethically. So, to overcome some of the issues, the authors designed a way to modify pixel data that would hold the hidden information. The objective of this work is to change the pixel values in a way that can be used to store information about black and white image pixel data. Prior to encryption and decryption, by using Python we were able to construct a passcode with hand gestures in the air, then encrypt it without any data loss. It concentrates on keeping track of simply two pixel values. Thus, pixel values are slightly changed to ensure the masked image is not misleading. Considering that the RGB values are at their border values of 254, 255 the test cases of masking overcome issues with the corner values susceptibility.
Article Details
References
D. Lerch-Hostalot and D. Megías, “LSB matching steganalysis based on patterns of pixel differences and random embedding,” Comput Secur, vol. 32, 2013, doi: 10.1016/j.cose.2012.11.005.
M. N. Wu, M. H. Lin, and C. C. Chang, “A LSB substitution oriented image hiding strategy using genetic algorithms,” Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), vol. 3309, 2004, doi: 10.1007/978-3-540-30483-8_27.
S. Badr and P. Noufal, “Integrated Data Hiding and Compression Scheme Based on SMVQ and FoE Inpainting,” Procedia Technology, vol. 24, 2016, doi: 10.1016/j.protcy.2016.05.220.
C. C. Chang, T. D. Kieu, and W. C. Wu, “A lossless data embedding technique by joint neighboring coding,” Pattern Recognit, vol. 42, no. 7, 2009, doi: 10.1016/j.patcog.2008.11.040.
C. C. Chang, T. D. Kieu, and Y. C. Chou, “Reversible information hiding for VQ indices based on locally adaptive coding,” J Vis Commun Image Represent, vol. 20, no. 1, 2009, doi: 10.1016/j.jvcir.2008.08.005.
S. Lee, C. D. Yoo, and T. Kalker, “Reversible image watermarking based on integer-to-integer wavelet transform,” IEEE Transactions on Information Forensics and Security, vol. 2, no. 3, 2007, doi: 10.1109/TIFS.2007.905146.
S. I. Nipanikar and V. H. Deepthi, “Wavelet transform-based steganographic method for secure data communication using OFDM system,” International Journal of Intelligent Computing and Cybernetics, vol. 10, no. 3, 2017, doi: 10.1108/IJICC-11-2016-0051.
S. I. Nipanikar, V. Hima Deepthi, and N. Kulkarni, “A sparse representation based image steganography using Particle Swarm Optimization and wavelet transform,” Alexandria Engineering Journal, vol. 57, no. 4, 2018, doi: 10.1016/j.aej.2017.09.005.
T. Rabie, M. Baziyad, and I. Kamel, “Enhanced high capacity image steganography using discrete wavelet transform and the Laplacian pyramid,” Multimed Tools Appl, vol. 77, no. 18, 2018, doi: 10.1007/s11042-018-5713-2.
S. Hemalatha, U. D. Acharya, and A. Renuka, “Wavelet transform based steganography technique to hide audio signals in image,” in Procedia Computer Science, 2015. doi: 10.1016/j.procs.2015.03.207.
H. Wu, H. Wang, H. Zhao, and X. Yu, “Multi-layer assignment steganography using graph-theoretic approach,” Multimed Tools Appl, vol. 74, no. 18, 2015, doi: 10.1007/s11042-014-2050-y.
S. N. Mali, P. M. Patil, and R. M. Jalnekar, “Robust and secured image-adaptive data hiding,” Digital Signal Processing: A Review Journal, vol. 22, no. 2, 2012, doi: 10.1016/j.dsp.2011.09.003.
P. Wang, X. He, Y. Zhang, W. Wen, and M. Li, “A robust and secure image sharing scheme with personal identity information embedded,” Comput Secur, vol. 85, 2019, doi: 10.1016/j.cose.2019.04.010.
Z. Ni, Y. Q. Shi, N. Ansari, W. Su, Q. Sun, and X. Lin, “Robust lossless image data hiding designed for semi-fragile image authentication,” IEEE Transactions on Circuits and Systems for Video Technology, vol. 18, no. 4, 2008, doi: 10.1109/TCSVT.2008.918761.
Arun K Singh, “Steganography in Digital Images Using LSB Technique,” Journal of Xidian University, vol. 14, no. 5, pp. 1–5, 2020.
G. Swain, “A Steganographic Method Combining LSB Substitution and PVD in a Block,” in Procedia Computer Science, 2016. doi: 10.1016/j.procs.2016.05.174.
S. Gapper et al., “Data Hiding by LSB Substitution Using Genetic Optimal Key-Permutation.,” Inf Sci (N Y), vol. 2, no. 3, 2016.
R. Karaki?, I. Güler, I. Çapraz, and E. Bilir, “A novel fuzzy logic-based image steganography method to ensure medical data security,” Comput Biol Med, vol. 67, 2015, doi: 10.1016/j.compbiomed.2015.10.011.
B. L. Lai and L. W. Chang, “Adaptive data hiding for images based on Harr Discrete Wavelet Transform,” in Lecture Notes in Computer Science (including subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics), 2006. doi: 10.1007/11949534_109.
M. Juneja and P. S. Sandhu, “An Improved LSB Based Steganography Technique for RGB Color Images,” International Journal of Computer and Communication Engineering, 2013, doi: 10.7763/ijcce.2013.v2.238.
Z. Ni, Y. Q. Shi, N. Ansari, and W. Su, “Reversible data hiding,” IEEE Transactions on Circuits and Systems for Video Technology, vol. 16, no. 3, 2006, doi: 10.1109/TCSVT.2006.869964.
Q. Li, B. Yan, H. Li, and N. Chen, “Separable reversible data hiding in encrypted images with improved security and capacity,” Multimed Tools Appl, vol. 77, no. 23, 2018, doi: 10.1007/s11042-018-6187-y.
C. K. Chan and L. M. Cheng, “Hiding data in images by simple LSB substitution,” Pattern Recognit, vol. 37, no. 3, 2004, doi: 10.1016/j.patcog.2003.08.007.
K. Upendra Raju and N. Amutha Prabha, “Dual images in reversible data hiding with adaptive color space variation using wavelet transforms,” International Journal of Intelligent Unmanned Systems, vol. 11, no. 1, 2023, doi: 10.1108/IJIUS-08-2021-0095.
F. A. Al-Omari, O. D. Al-Khaleel, G. A. Rayyashi, and S. H. Ghwanmeh, “An innovative information hiding technique utilizing cumulative peak histogram regions,” Journal of Systems and Information Technology, vol. 14, no. 3, 2012, doi: 10.1108/13287261211255356.
M. A. Pratt, S. Konda, and C. H. Henry Chu, “Texture-based image steganalysis by artificial neural networks,” International Journal of Intelligent Computing and Cybernetics, vol. 1, no. 4, 2008, doi: 10.1108/17563780810919122.
T. C. Lu, C. C. Chang, and Y. H. Huang, “High capacity reversible hiding scheme based on interpolation, difference expansion, and histogram shifting,” Multimed Tools Appl, vol. 72, no. 1, 2014, doi: 10.1007/s11042-013-1369-0.
S. Y. Shen and L. H. Huang, “A data hiding scheme using pixel value differencing and improving exploiting modification directions,” Comput Secur, vol. 48, 2015, doi: 10.1016/j.cose.2014.07.008.