Security Enhancement in Surveillance Cloud Using Machine Learning Techniques
Main Article Content
Abstract
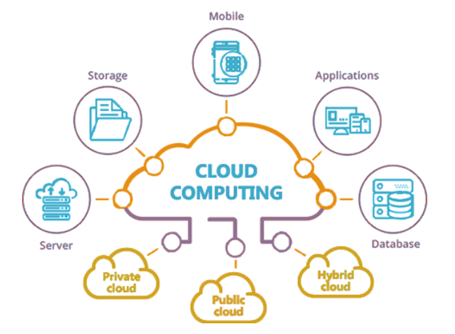
Most industries are now switching from traditional modes to cloud environments and cloud-based services. It is essential to create a secure environment for the cloud space in order to provide consumers with a safe and protected environment for cloud-based transactions. Here, we discuss the suggested approaches for creating a reliable and safe environment for a surveillance cloud. When assessing the security of vital locations, surveillance data is crucial. We are implementing machine learning methods to improve cloud security to more precisely classify image pixels, we make use of Support Vector Machines (SVM) and Fuzzy C-means Clustering (FCM). We also extend the conventional two-tiered design by adding a third level, the CloudSec module, to lower the risk of potential disclosure of surveillance data.In our work we evaluates how well our proposed model (FCM-SVM) performed against contemporary models like ANN, KNN, SVD, and Naive Bayes. Comparing our model to other cutting-edge models, we found that it performed better, with an average accuracy of 94.4%.
Article Details
References
Marwan, Mbarek, Ali Kartit, and Hassan Ouahmane. "Security enhancement in healthcare cloud using machine learning." Procedia Computer Science 127 (2018): 388-397.
Nassif, Ali Bou, Manar Abu Talib, Qassim Nasir, Halah Albadani, and Fatima Mohamad Dakalbab. "Machine learning for cloud security: a systematic review." IEEE Access 9 (2021): 20717-20735.
Mohanty, Sachi Nandan, Gouse Baig Mohammad, Sirisha Potluri, P. Ramya, and P. Lavanya. "Next Generation Cloud Security: State of the Art Machine Learning Model." Cloud Security: Techniques and Applications 1 (2021): 125.
Mohammad, Abdul Salam, and Manas Ranjan Pradhan. "Machine learning with big data analytics for cloud security." Computers & Electrical Engineering 96 (2021): 107527.
Srikanth, N., and T. Prem Jacob. "An Real Time Cloud Security System and Issues comparison using Machine and Deep Learning." In 2021 Fifth International Conference on I-SMAC (IoT in Social, Mobile, Analytics and Cloud)(I-SMAC), pp. 523-529. IEEE, 2021.
Salman, Tara, Deval Bhamare, Aiman Erbad, Raj Jain, and Mohammed Samaka. "Machine learning for anomaly detection and categorization in multi-cloud environments." In 2017 IEEE 4th international conference on cyber security and cloud computing (CSCloud), pp. 97-103. IEEE, 2017.
Gupta, Ishu, Rishabh Gupta, Ashutosh Kumar Singh, and Rajkumar Buyya. "MLPAM: A machine learning and probabilistic analysis based model for preserving security and privacy in cloud environment." IEEE Systems Journal 15, no. 3 (2020): 4248-4259.
Ding, Aaron Yi. "Mec and cloud security." Wiley 5G Ref: The Essential 5G Reference Online (2019): 1-16.
Karthika, P., and P. Vidhya Saraswathi. "IoT using machine learning security enhancement in video steganography allocation for Raspberry Pi." Journal of Ambient Intelligence and Humanized Computing 12, no. 6 (2021): 5835-5844.
Tiwari, Chandra Shekhar, and Vijay Kumar Jha. "Enhancing Security of Medical Image Data in the Cloud Using Machine Learning Technique." International Journal of Image, Graphics and Signal Processing (2022): 13-31.
Mohanta, Bhabendu Kumar, Debasish Jena, Utkalika Satapathy, and Srikanta Patnaik. "Survey on IoT security: Challenges and solution using machine learning, artificial intelligence and blockchain technology." Internet of Things 11 (2020): 100227.
Cohen, Aviad, and Nir Nissim. "Trusted detection of ransomware in a private cloud using machine learning methods leveraging meta-features from volatile memory." Expert Systems with Applications 102 (2018): 158-178.
Xiao, Liang, Xiaoyue Wan, Xiaozhen Lu, Yanyong Zhang, and Di Wu. "IoT security techniques based on machine learning: How do IoT devices use AI to enhance security?." IEEE Signal Processing Magazine 35, no. 5 (2018): 41-49.
Schelter, Sebastian, Felix Biessmann, Tim Januschowski, David Salinas, Stephan Seufert, and Gyuri Szarvas. "On challenges in machine learning model management." (2015).
Chiba, Zouhair, Noreddine Abghour, Khalid Moussaid, and Mohamed Rida. "Intelligent approach to build a Deep Neural Network based IDS for cloud environment using combination of machine learning algorithms." computers & security 86 (2019): 291-317.
Aldallal, Ammar, and Faisal Alisa. "Effective Intrusion Detection System to Secure Data in Cloud Using Machine Learning." Symmetry 13, no. 12 (2021): 2306.
Panker, Tomer, and Nir Nissim. "Leveraging malicious behavior traces from volatile memory using machine learning methods for trusted unknown malware detection in Linux
Qureshi, Basit, and Anis Koubâa. "Five traits of performance enhancement using cloud robotics: A survey." Procedia Computer Science 37 (2014): 220-227.cloud environments." Knowledge-Based Systems 226 (2021): 107095.
Natarajan, Jayapandian. "Cyber secure man-in-the-middle attack intrusion detection using machine learning algorithms." In AI and Big Data’s Potential for Disruptive Innovation, pp. 291-316. IGI global, 2020.
Mishra, Narendra, R. K. Singh, and Sumit Kumar Yadav. "Design a New Protocol for Vulnerability Detection in Cloud Computing Security Improvement." In Proceedings of the International Conference on Innovative Computing & Communication (ICICC). 2021.
Sangui, Smarta, and Swarup Kr Ghosh. "Cloud Security Using Honeypot Network and Blockchain: A Review." Machine Learning Techniques and Analytics for Cloud Security (2021): 213-237.
Rath, Mamata, and Sushruta Mishra. "Advanced-level security in network and real-time applications using machine learning approaches." In Research Anthology on Machine Learning Techniques, Methods, and Applications, pp. 664-680. IGI Global, 2022.
Quraishi, Suhail Javed. "Machine Learning Approach for Cloud Computing Security." In 2022 3rd International Conference on Intelligent Engineering and Management (ICIEM), pp. 158-163. IEEE, 2022.
Tiwari, Pradeep Kumar, K. Kannan, Duggineni Veeraiah, Nikhil Ranjan, Jain Singh, Ghalib H. Alshammri, and Awal Halifa. "Security Protection Mechanism in Cloud Computing Authorization Model Using Machine Learning Techniques." Wireless Communications and Mobile Computing 2022 (2022).
Hema, C., and Fausto Pedro Garcia Marquez. "Storage Enhancement in the Cloud Using Machine Learning Technique and Novel Hash Algorithm for Cloud Data Security." In International Conference on Management Science and Engineering Management, pp. 516-526. Springer, Cham, 2022.
Alrashdi, Ibrahim, Ali Alqazzaz, Esam Aloufi, Raed Alharthi, Mohamed Zohdy, and Hua Ming. "Ad-iot: Anomaly detection of iot cyberattacks in smart city using machine learning." In 2019 IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), pp. 0305-0310. IEEE, 2019.
Uppal, Mudita, Deepali Gupta, Sapna Juneja, Adel Sulaiman, Khairan Rajab, Adel Rajab, M. A. Elmagzoub, and Asadullah Shaikh. "Cloud-Based Fault Prediction for Real-Time Monitoring of Sensor Data in Hospital Environment Using Machine Learning." Sustainability 14, no. 18 (2022): 11667.
Thenappan, S., M. Valan Rajkumar, and P. S. Manoharan. "Predicting diabetes mellitus using modified support vector machine with cloud security." IETE Journal of Research (2020): 1-11.
Ali, Elmustafa Sayed, Mohammad Kamrul Hasan, Rosilah Hassan, Rashid A. Saeed, Mona Bakri Hassan, Shayla Islam, Nazmus Shaker Nafi, and Savitri Bevinakoppa. "Machine learning technologies for secure vehicular communication in internet of vehicles: recent advances and applications." Security and Communication Networks 2021 (2021).
Vora, Utsav, Jayleena Mahato, Hrishav Dasgupta, Anand Kumar, and Swarup Kr Ghosh. "Machine Learning–Based Security in Cloud Database—A Survey." Machine Learning Techniques and Analytics for Cloud Security (2021): 239-269.
Mondal, Avijit, and Radha Tamal Goswami. "Enhanced Honeypot cryptographic scheme and privacy preservation for an effective prediction in cloud security." Microprocessors and Microsystems 81 (2021): 103719.
Mondal, Avijit, and Radha Tamal Goswami. "Enhanced Honeypot cryptographic scheme and privacy preservation for an effective prediction in cloud security." Microprocessors and Microsystems 81 (2021): 103719.
Muddala, Saikrishna, and Charanya Ramakrishnan. "Review of Face Recognition Techniques for Secured Cloud Data Surveillance using Machine Learning." In 2020 5th International Conference on Innovative Technologies in Intelligent Systems and Industrial Applications (CITISIA), pp. 1-10. IEEE, 2020.
Zekri, Marwane, Said El Kafhali, Noureddine Aboutabit, and Youssef Saadi. "DDoS attack detection using machine learning techniques in cloud computing environments." In 2017 3rd international conference of cloud computing technologies and applications (CloudTech), pp. 1-7. IEEE, 2017.
Chkirbene, Zina, Aiman Erbad, Ridha Hamila, Ala Gouissem, Amr Mohamed, and Mounir Hamdi. "Machine learning based cloud computing anomalies detection." IEEE Network 34, no. 6 (2020): 178-183.
Alshammari, Amirah, and Abdulaziz Aldribi. "Apply machine learning techniques to detect malicious network traffic in cloud computing." Journal of Big Data 8, no. 1 (2021): 1-24.
Reddy, SaiSindhuTheja, and Gopal K. Shyam. "A machine learning based attack detection and mitigation using a secure SaaS framework." Journal of King Saud University-Computer and Information Sciences (2020).
Diener, Michael, Leopold Blessing, and Nina Rappel. "Tackling the cloud adoption dilemma-A user centric concept to control cloud migration processes by using machine learning technologies." In 2016 11th International Conference on Availability, Reliability and Security (ARES), pp. 776-785. IEEE, 2016.
Rath, Mamata, Jyotirmaya Satpathy, and George S. Oreku. "Artificial intelligence and machine learning applications in cloud computing and internet of things." In Artificial intelligence to solve pervasive internet of things issues, pp. 103-123. Academic Press, 2021.
Sharma, Abhishek, and Umesh Kumar Singh. "Modelling of Smart Risk Assessment Approach for Cloud Computing Environment using AI & supervised machine learning algorithms." Global Transitions Proceedings (2022).
Kumar, Yogesh, Surabhi Kaul, and Yu-Chen Hu. "Machine learning for energy-resource allocation, workflow scheduling and live migration in cloud computing: State-of-the-art survey." Sustainable Computing: Informatics and Systems 36 (2022): 100780.
Kannagi, A., J. Gori Mohammed, S. Sabari Giri Murugan, and M. Varsha. "Intelligent mechanical systems and its applications on online fraud detection analysis using pattern recognition K-nearest neighbor algorithm for cloud security applications." Materials Today: Proceedings (2021).
Wallis, Kevin, Christoph Reich, Blesson Varghese, and Christian Schindelhauer. "QUDOS: quorum-based cloud-edge distributed DNNs for security enhanced industry 4.0." In Proceedings of the 14th IEEE/ACM International Conference on Utility and Cloud Computing, pp. 1-10. 2021.
Kishor, Amit, Chinmay Chakraborty, and Wilson Jeberson. "A novel fog computing approach for minimization of latency in healthcare using machine learning." (2021).
Sharkh, Mohamed Abu, Yong Xu, and Eric Leyder. "CloudMach: cloud computing application performance improvement through machine learning." In 2020 IEEE Canadian Conference on Electrical and Computer Engineering (CCECE), pp. 1-6. IEEE, 2020.
Sasirekha, S. P., N. Mohanasudaram, P. Sherubha, and V. Manikandan. "An Enhanced Vehicle to Cloud Communication by Prediction Based Machine Learning Approaches." In 2020 International Conference on Computing and Information Technology (ICCIT-1441), pp. 1-4. IEEE, 2020.
Tahsien, Syeda Manjia, Hadis Karimipour, and Petros Spachos. "Machine learning based solutions for security of Internet of Things (IoT): A survey." Journal of Network and Computer Applications 161 (2020): 102630.
Pop, Daniel. "Machine learning and cloud computing: Survey of distributed and saas solutions." arXiv preprint arXiv:1603.08767 (2016).
Pop, Daniel. "Machine learning and cloud computing: Survey of distributed and saas solutions." arXiv preprint arXiv:1603.08767 (2016).
Renugadevi, G., B. Raj Kumar, A. Karthikeyan, and E. Iohn Prince. "Improvement of health efficiency using cloud and machine learning." In AIP Conference Proceedings, vol. 2519, no. 1, p. 030074. AIP Publishing LLC, 2022.
Kale, Rahul Vishwanath, Bharadwaj Veeravalli, and Xiaoli Wang. "A Practicable Machine Learning Solution for Security-Cognizant Data Placement on Cloud Platforms." In Handbook of computer networks and cyber security, pp. 111-131. Springer, Cham, 2020.
Saran, Munish, Rajan Kumar Yadav, and Upendra Nath Tripathi. "Machine Learning based Security for Cloud Computing: A Survey." International Journal of Applied Engineering Research 17, no. 4 (2022): 332-337.
Hesamifard, Ehsan, Hassan Takabi, Mehdi Ghasemi, and Catherine Jones. "Privacy-preserving machine learning in cloud." In Proceedings of the 2017 on cloud computing security workshop, pp. 39-43. 2017.
Miao, Yinbin, Wei Zheng, Xiaohua Jia, Ximeng Liu, Kim-Kwang Raymond Choo, and Robert Deng. "Ranked Keyword Search over Encrypted Cloud Data Through Machine Learning Method." IEEE Transactions on Services Computing (2022).
Alzahrani, Ahmed Saeed. "An optimized approach-based machine learning to mitigate DDoS attack in cloud computing." International Journal of Engineering Research and Technology 13, no. 6 (2020): 1441-1447.
Yadav, Saumya, Rakesh Chandra Joshi, and Divakar Yadav. "Trustworthy Machine Learning for Cloud-Based Internet of Things (IoT)." In Transforming Management with AI, Big-Data, and IoT, pp. 155-167. Springer, Cham, 2022.
Almuzaini, Khalid K., Amit Kumar Sinhal, Raju Ranjan, Vikas Goel, Rajeev Shrivastava, and Awal Halifa. "Key Aggregation Cryptosystem and Double Encryption Method for Cloud-Based Intelligent Machine Learning Techniques-Based Health Monitoring Systems." Computational Intelligence and Neuroscience 2022 (2022).
Saran, Munish, Rajan Kumar Yadav, and Upendra Nath Tripathi. "Machine Learning based Security for Cloud Computing: A Survey." International Journal of Applied Engineering Research 17, no. 4 (2022): 338-344.
Angelopoulos, Angelos, Emmanouel T. Michailidis, Nikolaos Nomikos, Panagiotis Trakadas, Antonis Hatziefremidis, Stamatis Voliotis, and Theodore Zahariadis. "Tackling faults in the industry 4.0 era—a survey of machine-learning solutions and key aspects." Sensors 20, no. 1 (2019): 109.
Muthulakshmia, K., and K. Valarmathib. "Attaining Cloud Security Solution Over Machine Learning Techniques." Smart Intelligent Computing and Communication Technology 38 (2021): 246.
Kaur, Prableen, Manik Sharma, and Mamta Mittal. "Big data and machine learning based secure healthcare framework." Procedia computer science 132 (2018): 1049-1059.
Rajput, Deepak Singh, Saurabh Sharma, Shiv Kumar Tiwari, A. K. Upadhyay, and Ashish Mishra. "Medical data security using blockchain and machine learning in cloud computing." In Mathematical Modeling and Soft Computing in Epidemiology, pp. 347-374. CRC Press, 2020.
Hesamifard, Ehsan, Hassan Takabi, Mehdi Ghasemi, and Rebecca N. Wright. "Privacy-preserving machine learning as a service." Proc. Priv. Enhancing Technol. 2018, no. 3 (2018): 123-142.
Potluri, Sirisha, Katta Subba Rao, and Sachi Nandan Mohanty, eds. Cloud Security: Techniques and Applications. Vol. 1. Walter de Gruyter GmbH & Co KG, 2021.
Rajarajeswari, P., M. Sreevani, and P. Lalitha Suryakumari. "Secure Cloud Risk Architecture analysis for Mobile Banking system and its performance analysis based on Machine learning approaches." In Journal of Physics: Conference Series, vol. 2089, no. 1, p. 012007. IOP Publishing, 2021.