Analytical Model for Assessing the Impact of MANETs' Bottleneck Nodes
Main Article Content
Abstract
Objectives: Due to few resources, the most challenging task in mobile ad hoc networks is determining a route with the highest probability of success between a source and a destination. The objectives of this assignment are as follows: The limited power provided by batteries is one of the most significant challenges in routing. A great number of routing protocols have been devised to deal with the problem of limited battery power. Reliability, low energy consumption, and preferential treatment of nodes with greater energy levels are the cornerstones of the routing path made possible by these protocols. On the other hand, these protocols result in the creation of a bottleneck intermediate node, which is a node that must forward packets from numerous sources. The loss of packets is the most significant issue that emerges with a bottleneck intermediate node.
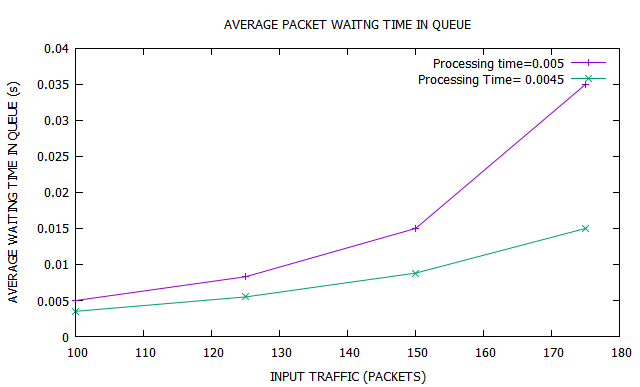
Methods and Statistical Analysis: In this study, we employ a poison random process to assess an intermediate's performance of bottleneck node within a mathematical model we developed. Findings: The model that is being proposed calculates the typical length of the queue at the input buffer, the typical amount of time spent waiting in the buffer and the lifetime of the network.
Application and enhancements: This model is put to use to regulate the incoming traffic of an intermediate node and to determine whether or not that node will participate in the route.
Article Details
References
. Mohammad, Arshad Ahmad Khan, Ali Mirza, and Mohammed Abdul Razzak. "Reactive energy aware routing selection based on knapsack algorithm (RER-SK)." In Emerging ICT for Bridging the Future-Proceedings of the 49th Annual Convention of the Computer Society of India CSI Volume 2, pp. 289-298. Springer, Cham, 2015.
. Sana, Afreen Begum, Farheen Iqbal, and Arshad Ahmad Khan Mohammad. "Quality of service routing for multipath manets." In 2015 International Conference on Signal Processing and Communication Engineering Systems, pp. 426-431. IEEE, 2015.
. Siddiqua, Ayesha, Kotari Sridevi, and Arshad Ahmad Khan Mohammed. "Preventing black hole attacks in MANETs using secure knowledge algorithm." 2015 International Conference on Signal Processing and Communication Engineering Systems. IEEE, 2015.
. Sultana, Towheed, Arshad Ahmad Khan Mohammad, and Nikhil Gupta. "Importance of the Considering Bottleneck Intermediate Node During the Intrusion Detection in MANET." In Research in Intelligent and Computing in Engineering, pp. 205-213. Springer, Singapore, 2021.
. Mohammad, Arshad Ahmad Khan, Ali Mirza Mahmood, and Srikanth Vemuru. "Intentional and unintentional misbehaving node detection and prevention in mobile ad hoc network." International Journal of Hybrid Intelligence 1, no. 2-3 (2019): 239-267.
. Mohammad, Arshad Ahmad Khan, Ali Mirza Mahmood, and Srikanth Vemuru. "Energy-Aware Reliable Routing by Considering Current Residual Condition of Nodes in MANETs." In Soft Computing in Data Analytics, pp. 441-452. Springer, Singapore, 2019.
. Mohammad, Arshad Ahmad Khan, Ali Mirza, and Srikanth Vemuru. "Cluster based mutual authenticated key agreement based on chaotic maps for mobile ad hoc networks." Indian Journal of Science and Technology 9 (2016): 26.
. Mohammad, Arshad Ahmad Khan, Ali Mirza, and Srikanth Vemuru. "Analytical Model for Evaluating the Bottleneck Node in MANETs." Indian Journal of Science and Technology 9 (2016): 31.
. Mohammad, Arshad Ahmad Khan, Ali Mirza, and Srikanth Vemuru. "Energy aware routing for manets based on current processing state of nodes." Journal of Theoretical and Applied Information Technology 91, no. 2 (2016): 340.
. Abdul, Arif Mohammad, Arshad Ahmad Khan Mohammad, P. Venkat Reddy, Praveena Nuthakki, Rakesh Kancharla, Rahul Joshi, and N. Kannaiya Raja. "Enhancing Security of Mobile Cloud Computing by Trust-and Role-Based Access Control." Scientific Programming (2022).
. Mohammad, Arshad Ahmad Khan, Et Al. "Efficient Mobile Sink Location Placement By Residual Status In WSN To Enhance The Network Lifetime." Journal of Engineering Science and Technology 16.6 (2021): 4779-4790.
. Sastry, M. Kiran, Arshad Ahmad Khan Mohammad, and Mohammad Abdul Arif. "Optimized Energy-efficient Load Balance Routing Protocol for Wireless Mesh Networks." International Journal of Advanced Computer Science and Applications 12.8 (2021).
. Arshad Ahmad Khan Mohammad, Towheed Sultana” Evaluation Of Performance Degradation Due To The Presence Of Bottleneck Intermediate Node In Communication Path In Manet” International Journal of Engineering and Advanced Technology (IJEAT) ISSN: 2249-8958 (Online), Volume-8 Issue-4, April 2019
. Mohammad Mohammad, Aleem Mohammed and C Atheeq, “Prior Bush Fire Identification Mechanism Based on Machine Learning Algorithms” International Journal of Artificial Intelligence and Applications, Vol.13, No.4, July 2022
. C Atheeq, M Munir Ahamed Rabbani, “CACK—A Counter Based Authenticated ACK to Mitigate Misbehaving Nodes from MANETs” Recent Advances in Computer Science and Communications 12, 2021.
. C Atheeq, M Munir Ahamed Rabbani, “Secure Data transmission in integrated internet MANETs based on effective trusted knowledge algorithm” Indian Journal of Science and Technology. Vol. 9 No. 47, Dec 2016
. C. Atheeq, Ahamed Rabbani, “Secure Intelligence Algorithm for data transmission in Integrated Internet MANET” International Journal of Computer Science and Applications, Vol. 14, No. 2, pp. 142 – 163, 2017.
. Ahmad A, Jalal S. Packet loss estimation using Poisson random process for improving multimedia transmission in MANETs. Advances in Computing, Communications and Informatics (ICACCI), International Conference on. IEEE, Mysore, 2013, pp. 661-666.